Data Security & Storage

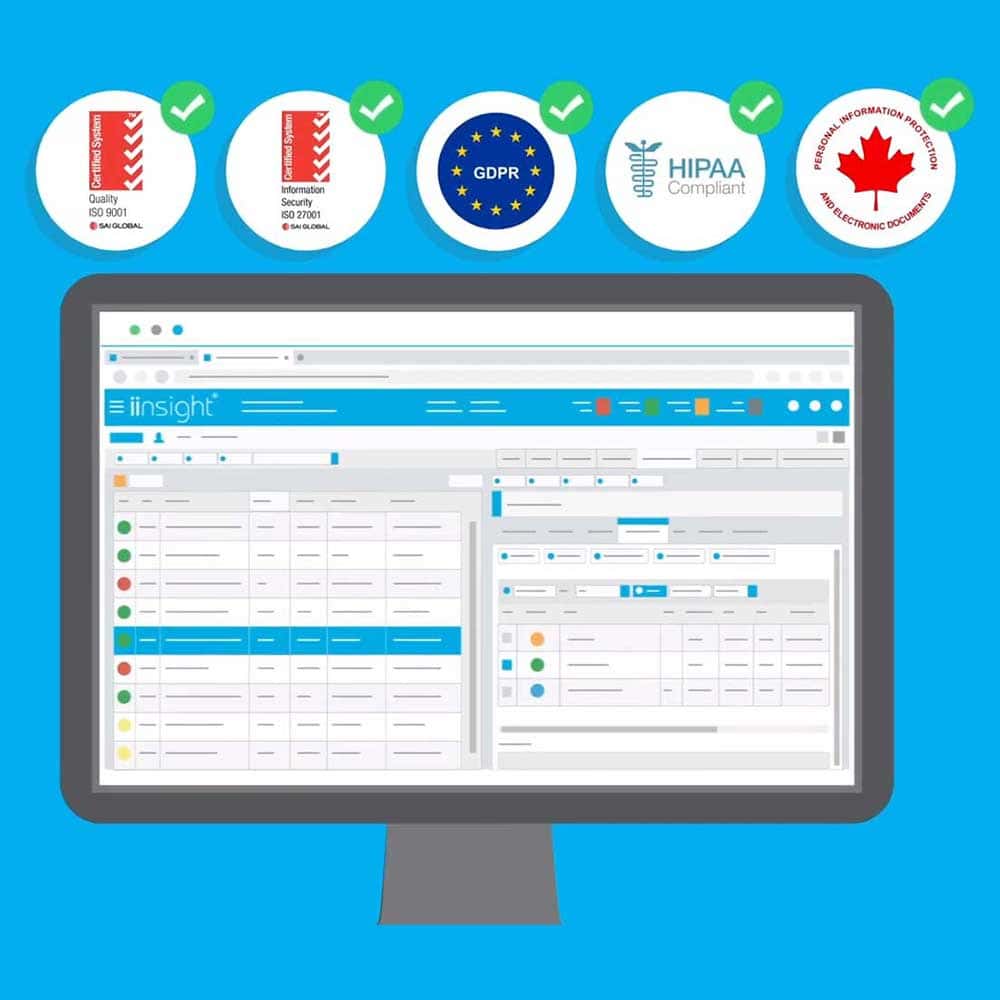
Accreditations and Compliance
We take compliance seriously and undergo external audits annually to ensure adherence to industry standards. Our accreditations include:
- ISO9001:2015 (Quality Management Systems) – Australia/New Zealand/International
- ISO27001:2013 (Information Security Management Systems) – Australia/New Zealand/International
- GDPR (General Data Protection Regulation) – United Kingdom and European Union
- HIPAA (Health Insurance Portability and Accountability Act) – United States
- PIPEDA (Personal Information Protection and Electronic Documents Act) - Canada
At iinsight®, we understand the importance of data protection and security for our customers. We store our client’s data across three data centres (availability zones) in each of the seven countries we serve. By partnering with Amazon Web Services (AWS), we maintain a local presence and comply with data retention regulations in each country. Which means that your data will NEVER leave the country of origin. Our distributed storage infrastructure guarantees software, hardware, and data centre level redundancy, providing a remarkable uptime of 99.999%.
Leverage off our Compliance & Accreditation!
& complimentary assistance from our compliance team!
iinsight® often has clients who are approached by their various funding bodies. These funding bodies request certain documents and information, such as auditability, due diligence, and security questionnaires, to be completed and returned by a specified deadline.
The Due Diligence and Security Questionnaires that the funding bodies request often contain technical questions related to client data, its storage, and the security measures in place to protect that data. These questionnaires likely seek detailed information about how the client's data is handled, stored, and safeguarded to ensure compliance with data protection regulations and to address any potential risks or vulnerabilities.
To make this process easier for providers, iinsight® offers a complimentary service to its customers. You can simply contact our compliance team, who will respond on your behalf and provide you with all the supporting literature. The best part is that this service comes at no additional cost to our customers.
All iinsight® customers can benefit from leveraging our Compliance Certifications and Accreditations. By having these certifications, our customers can enhance their business prospects, such as increasing their chances of securing contracts through applications for tenders or responding to Request for Proposals (RFPs). iinsight®'s certifications and accreditations can serve as valuable credentials that demonstrate adherence to compliance and security standards, giving you a competitive advantage in the market.
- Local data centres and backups
We provide services in 7 countries and partner with AWS (Amazon Web Services). This provides a local presence of data retention and storage in each of these countries. Data never leaves the country of origin. In each country we store client’s data across 3 data centres (called availability zones in AWS), so our clients have redundancy at software, hardware, and data centre levels. This allows us to provide an uptime of 99.99%
- Data Backups Every 5 Minutes
We understand the importance of real-time data integrity. That's why we perform backups of your critical data every 5 minutes, capturing any changes or updates made within that timeframe. This frequent backup schedule ensures minimal data loss in the event of an unforeseen incident.
- Collateral Backups Every Hour
In addition to data backups, we also prioritise the protection of your collateral, which includes various file types such as video files and other important assets. We perform backups of all collateral files on an hourly basis, ensuring that your valuable content remains safe and accessible.
- Data Encryption
The security of your data is paramount to us. All data within the iinsight® platform, including documents and client collateral, is encrypted in transit and at rest using TLS 1.2, ensuring secure transmission and storage.
- Privacy and Single Tenancy
We operate under a single tenanted model, providing each organisation on the iinsight® platform with its own private database and document repository. Our operations comply with the Privacy Act 1988, which is further evidenced in our ISO 27001 and ISO 9001 Integrated Management System Policies and Procedures.
- 24x7 Monitoring and Maintenance
To mitigate potential threats, we maintain a 24x7 monitoring and maintenance arrangement. Our dedicated staff promptly responds to monitoring software alerts, and we collaborate with AWS to monitor web application firewalls and load balancers, proactively blocking access from unwarranted IP addresses.
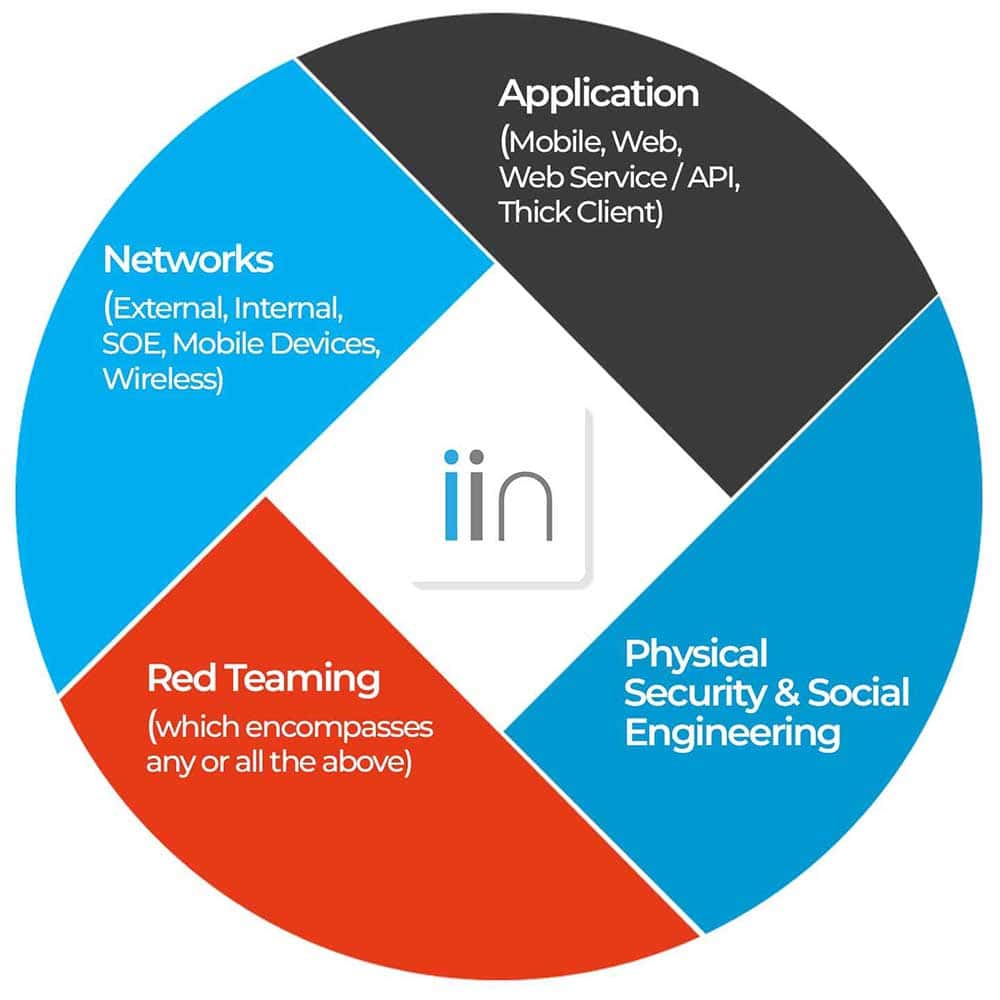
Quarterly third-party Web Application Penetration Testing (PEN)
- to identify vulnerabilities and ensure robust security.
Regular Security Assessments
We prioritise proactive security measures through third-party engagements. Artifice Security conducts quarterly Web Application Penetration Testing (PEN) to identify vulnerabilities and ensure robust security.
Additionally, we leverage a third-party automation software that performs deep code vulnerability testing, conforming to the OWASP standards.
These assessments occur fortnightly and are reviewed diligently.